From geopolitics to advancing technology, there are several reasons why 2022 is a crucial time to tighten up your cybersecurity plan.
Cyberattacks in 2022 are so much more than obviously suspicious phishing email scams, and your team needs to be privy to all of the threats that may come across their devices.
Here are some of the most prominent cybersecurity threats to know about in 2022.
Cryptojacking
It’s hard to walk into a small-talk situation without briefly touching on the state of cryptocurrency. Thanks to the intriguing and lucrative nature of crypto, it’s at the front of everyone’s mind — especially hackers.
With the growing popularity of owning crypto, hackers can use a victim’s computing power to generate cryptocurrency.
This threat embeds in a victim’s device and uses its resources to mine crypto. Unlike other cyberattacks, this method is meant to stay hidden from the victim.
Reports of cryptojacking usually increase when the value of crypto increases. So when you see those spikes in value, be aware of what’s running on your devices.
Social Engineering
Social engineering is a tactic where hackers phish for important info via email, phone or in person. The goal is to obtain sensitive information that helps gain a back door into a digital system.
No, social engineering attacks are not new. But, social engineering can catch even the most vigilant employees off guard, as most people expect a phishing attempt to look like a scammy email. But, social engineering can look much more convincing than that.
In an example of the effectiveness of social engineering, one social engineer hacker gained access to one (willing) victim’s sensitive info by impersonating a frantic wife needing her husband’s information.
Do your employees know to look out for this? Make sure everyone needs to enter, send or speak a verification method before sharing sensitive info.
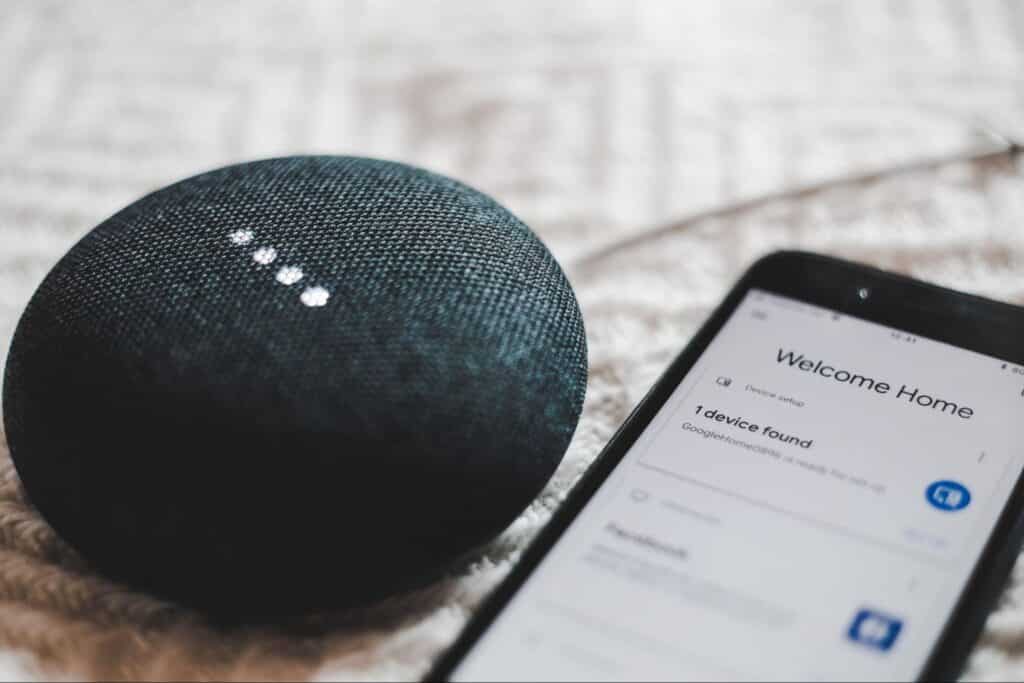
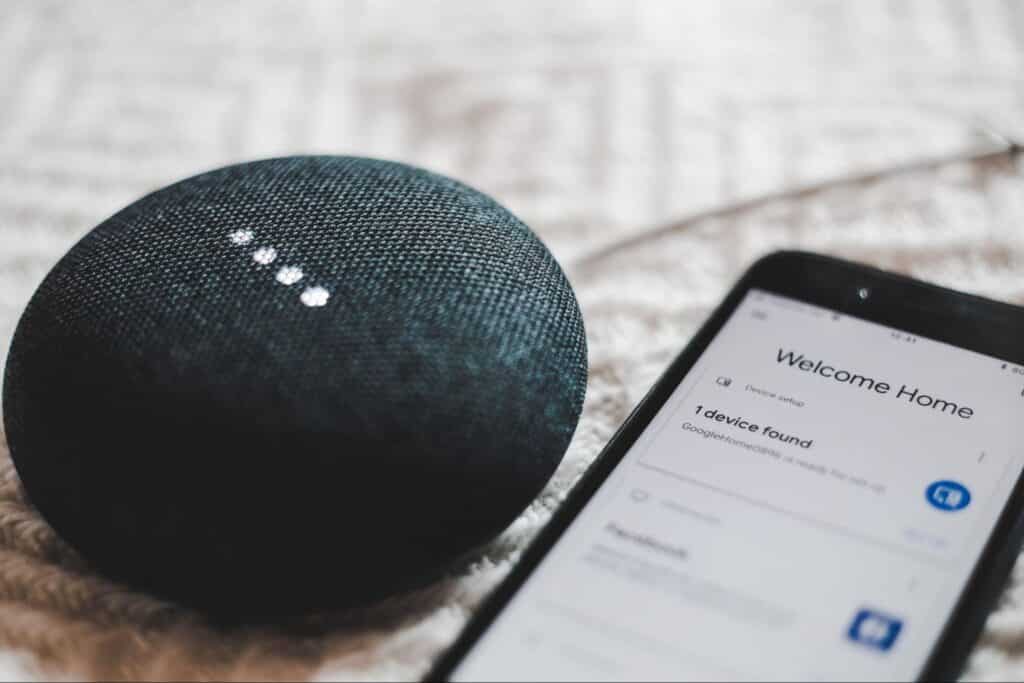
Smart Appliances
Personal residences and corporate offices can rely heavily on smart appliances to handle daily tasks. From printers to refrigerators, devices that connect to WiFi suddenly become a potential backdoor for hackers.
Seventy percent of homes and even more offices have a smart device on the premises. That means both office and remote workers hold a small risk of a cyberattack through the Internet of Things. In addition, if your workers have poor “digital hygiene” habits in their work environment and with personal devices, there can be a risk of potential cyberattacks.
Studies predict that the number of smart devices in homes and offices will double between 2021 and 2025 — so the opportunity to hack smart devices will also increase.
Poor Data Management
Did you know that the data generated by consumers doubles every four years? So 2022 is the year to nail down your data management.
Piles upon piles of unorganized data can confuse employees and create vulnerabilities in your digital presence. As data breaches in the U.S. can cost as much as $9.05 million in 2021, practical data storage and organization are crucial.
The key to strong and secure data management is data recovery, adequate cloud storage and high capacity transport. This trifecta allows you to share information safely, store data effectively and have a confident backup plan if anything happens.
Mobile Device Vulnerabilities
From malicious apps to mobile phishing emails, phones are just as big a hacking opportunity, if not more significant.
Smartphones have just as much ability to download files and applications as desktops do and have access to sensitive information. The difference between desktops and phones is that potential victims have their phones in their hands, surfing the web almost 24/7. With that numbers game, the chances that someone will eventually fall victim to a mobile phone is pretty good.
Another unique vulnerability with smartphones is “smishing” — or phishing scams over text. Text messages are much more likely to get immediately opened than emails, and studies show that victims are more likely to trust and click on text links over email.
These chances of opening and level of trust have directly contributed to how smishing attacks have risen 328% in 2020 alone.

Unhappy Employees
With a deep understanding of known data processes and admin access, disgruntled employees can wreak havoc on your digital presence.
Your employees are your most valuable asset and can also be your most dangerous cyber threat. A single employee or ex-employee can badly impact businesses of all sizes with a malicious goal.
But, that is not to say that you shouldn’t trust your employees. The way to reduce the chances of a disgruntled employee is by focusing on a positive work environment and working to end each processional relationship amicably.
But we all know that out of dozens of employees that leave, one or two won’t quit on excellent terms. So to account for those times, all employees should follow a comprehensive and instantaneous offboarding process that happens the moment the employee cuts ties with the company.
Third-Party Risk
Giving cloud and system access to third-party companies is often necessary but needs to be done carefully to mitigate significant cyber risk. This is particularly important in 2022, as most companies work with remote partners (so logins are sent digitally) and leverage third-party companies for marketing, IT, data management and consulting… The list is a long one.
The more log-ins, cloud data and accounts created or shared, the more chance of log-ins following into the wrong hands. So one way to cut down on third-party security threats is only to give access when necessary and never give admin access unless completely necessary.
Multi-Cloud Hopping
One threat that feels like a catch-22 is hackers taking advantage of multi-cloud hopping.
Leveraging cloud storage has many benefits — but they are not without their unique risks. Multi-cloud hopping is a hacking method of jumping between one cloud and another within a company that has a multiple-cloud structure. A hacker can potentially reach farther, finding more sensitive data and more opportunities with the more cloud info they find access.
As 76% of companies are multi-cloud, it’s crucial to have the right resources to stamp down on this version of hacking.

How to Protect Yourself
Secure cloud services – Cloud storage has too many benefits to ignore, even though it can pose a data breach risk. Secure cloud services, along with competent data processes, maximize benefits and minimize risks — so you can be confident in the status of your data management.
Effective disaster recovery – Stuff happens. When it does, a dependable disaster recovery plan can save you from losing time, money, sanity and, of course, data. Data recovery in a secure, environmentally-controlled third-party storage will give you peace of mind, no matter what challenges arise.
Proactive maintenance – With all of the third-party tools and plugins most applications have, proactive maintenance protects against cyberattacks. This effort maximizes protection against malicious attacks and reduces maintenance costs, breakdowns and downtime.
Current cybersecurity tools and training – An informed and educated team is your most essential tool against cyberattacks. From strong password security to following a verification process to being vigilant with what links to trust, your employees can cut down on many chances for hacking. In addition, working with experts on setting up a cybersecurity plan and training your team will round out your protection and help everyone be confident in handling sensitive data.
2022 is a year of global cyber threats and new places to find them. When this is too big of a task to handle internally, MDL has your back.
Your company’s security is our top priority. We offer 24/7 support, network monitoring, offsite data backups, auditing and compliance and more to help ensure that you don’t need to stress about your team’s private information becoming public.







